ONE PLATFORM, FOR ALL YOUR NEEDS
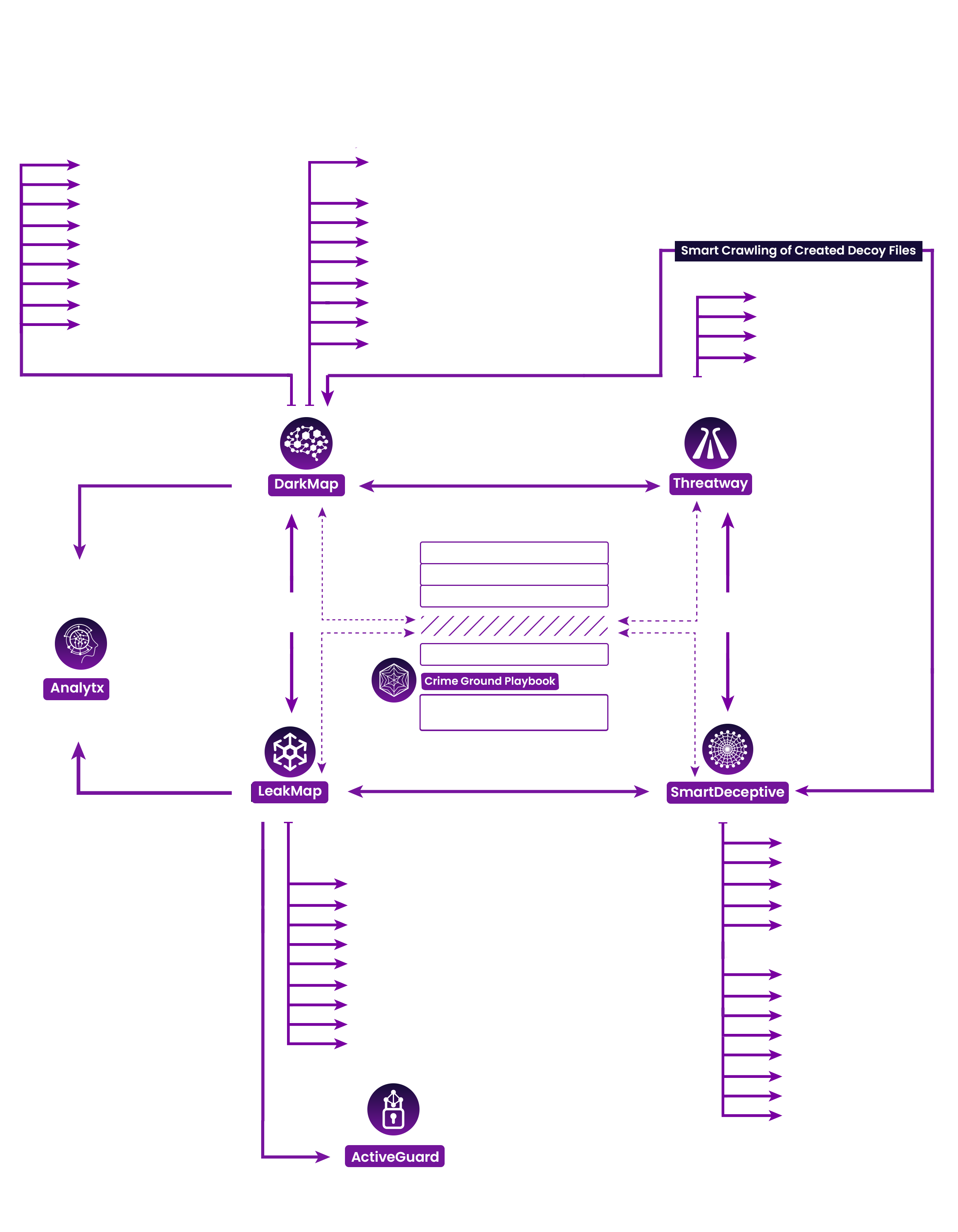
CATCHPROBE offers web intelligence, threat intelligence, detection, deception and leaked data profiling services, and response features deployed on the same platform, working fast and in harmony with each other.
Analogous to how you would monitor your home with a camera, you must do the same with your data in the digital world. The camera can't prevent a break-in, but it can help you know who did it, and what they did. You might not have control over what goes on in the digital world, but you can protect yourself by being aware and using a combination of tools to take precautions and, more importantly, to prevent damage. Our product provides an amazing platform for institutions, governments, and individuals. Because everyone needs verified intelligence.
LESSEN THE BURDEN OF TASKS
All services on the platform are readily available and their uses are easily comprehensible, allowing you to begin using it even without the help of security operations professionals.

HAVE US HANDLE THE LOAD
Cut your expenses on the otherwise unjustifiably necessary and high-priced hardware.
DIVE IN AND LEARN
Get to know your attackers and safely watch what they are attacking to.